Most guidance on insider threat detection assumes you have resources you don't have. A Security Operations Center. Dedicated analysts. Time to write detection rules, tune thresholds, and investigate alerts. Budget for enterprise-grade tools that require months of implementation.
If you're running a lean IT team, none of that applies. You're managing infrastructure, handling support tickets, evaluating vendors, and keeping systems operational. Building a traditional insider threat program isn't just difficult. It's unrealistic.
But the threats don't care about your team size. A departing employee can exfiltrate data just as easily at a 200-person company as at a 20,000-person enterprise. A compromised account moves laterally through your environment regardless of whether you have analysts watching for it. Accidental exposure happens when someone finds a workaround to share files quickly, whether you have the resources to monitor it or not.
The good news? You don't need a SOC to build effective insider threat detection. You need the right approach, the right tools, and a clear understanding of what matters for your organization.
Here's how to build an insider threat program that works for lean teams.
Step 1: Understand Your Exposure
Before you can detect threats, you need to know what you're protecting and where your biggest risks live.
Start by identifying where sensitive data exists in your environment. Customer information, financial records, intellectual property, employee data, proprietary processes. What systems hold this data? Who has access? How is it typically used?
You don't need a formal data classification program or months of discovery. You need a clear picture of your critical assets. What would hurt most if it walked out the door? What would regulators care about if it got exposed? What would your customers lose trust over if it ended up in the wrong hands?
Next, identify your highest-risk scenarios. Every organization has different pressure points. For some, it's departing employees in competitive industries. For others, it's contractors with temporary access to sensitive systems. For many, it's admin accounts that become high-value targets if compromised.
Think about your specific context. Do you have people with access to customer databases who interact with competitors? Do you grant temporary access to consultants or vendors who work on sensitive projects? Do you have remote employees accessing systems from various locations? Do your finance or HR teams handle data that could be valuable to external parties?
You're not trying to map every possible risk. You're identifying the scenarios that are most likely and most damaging for your organization specifically.
Step 2: Define What Detection Needs to Catch
Once you understand your exposure, you can define what your detection should catch. This isn't about listing every possible threat. It's about focusing on the scenarios that matter most for your organization.
For most lean teams, this comes down to three categories:
- Data exfiltration. Can you detect when someone is moving large volumes of sensitive data out of your environment? This includes bulk downloads, files emailed to external addresses, uploads to personal cloud storage, or data copied to removable media.
- Compromised accounts. Can you detect when a legitimate account starts behaving unusually? This includes logins from unexpected locations or times, access to files or systems the user doesn't normally touch, or sudden changes in activity patterns that suggest someone else is using the credentials.
- High-risk user activity. Can you detect when insiders are taking actions that create exposure, whether malicious or accidental? This includes accessing sensitive data during notice periods, sharing credentials, storing passwords in insecure locations, or using unauthorized tools and services.
The key is focusing on behaviors that indicate risk, not trying to monitor everything. You need detection that's targeted enough to be actionable but broad enough to catch the scenarios that matter.
Step 3: Choose Detection That Works for Lean Teams
This is where most traditional approaches fall apart. Enterprise tools assume you have analysts to configure rules, tune alerts, and investigate findings. Rule-based systems require someone to define what's suspicious, maintain those definitions as your environment changes, and sort through false positives to find real threats.
You need detection that works differently. Specifically, you need tools that:
- Deploy quickly. Months of implementation and configuration aren't realistic. You need something that integrates with your existing environment and starts working immediately. If it takes more than a few hours to get up and running, it's not built for lean teams.
- Learn automatically. You don't have time to write detection rules or define baseline behavior manually. The system should observe your environment, learn what normal looks like for each user, and flag deviations without requiring ongoing tuning.
- Provide clear context. When something is flagged, you shouldn't need a background in threat analysis to understand what happened. Alerts should explain what was accessed, when it occurred, why it's unusual for this specific user, and what evidence supports the finding.
- Adapt as your organization changes. People change roles, workflows evolve, new tools get adopted. Your detection should adjust automatically without requiring manual updates every time something shifts.
Behavior-based detection using AI meets these requirements. It learns normal patterns for each user across your cloud environment, flags anomalies automatically, and provides the context you need to assess risk and respond appropriately. No rules to write, no thresholds to tune, no analysts required.
Step 4: Build Your Response Process
Detection only matters if you can respond effectively. You don't need a formal incident response team or a 50-page playbook. You need clarity on who gets alerted when something is detected, and what happens next.
Start by defining alert routing. Who should be notified when suspicious behavior is detected? For most lean teams, this is the IT manager or head of IT, potentially with escalation to a CTO or CISO for high-severity findings. The key is making sure alerts reach someone who can act, not disappearing into a queue no one monitors.
Next, establish a basic escalation process. What happens when an alert comes in? Who investigates? What information do they need? When should HR be involved? When should legal be consulted? This doesn't need to be complicated, but it should be defined before you're in the middle of an incident.
Finally, document basic response actions for common scenarios. If a departing employee is flagged for downloading sensitive files, what's the immediate response? If an admin account shows signs of compromise, what steps do you take? If someone accidentally exposes data externally, how do you contain it?
You're not writing a comprehensive incident response plan. You're creating enough structure that your team knows what to do when detection surfaces a real issue.
Step 5: Measure What Matters
You need visibility into whether your detection is working, but traditional security metrics don't apply to lean teams. You're not measuring mean time to detect or tracking analyst productivity. You're measuring whether the program is sustainable and effective.
Focus on three things:
- Coverage. Are you monitoring the systems and data that matter? If your sensitive data lives in Microsoft 365 and you're only monitoring on-premises file shares, you have a gap.
- Signal quality. What percentage of alerts are actionable? If you're getting dozens of alerts per day and most are false positives, something is wrong. Good detection should surface 5-10 alerts per week where most warrant investigation.
- Response capability. When something is detected, can your team actually respond? If alerts are too complex to understand or lack the context needed to investigate, your detection isn't working regardless of how sophisticated it is.
These metrics tell you if your program is functioning. They're not about demonstrating ROI to executives or justifying budget. They're about ensuring your limited resources are focused on detection that protects your organization.
Common Pitfalls to Avoid
- Over-engineering. Don't try to build an enterprise-grade program. You're not an enterprise. Focus on the scenarios that matter most and accept that you won't catch everything. Good enough beats perfect every time when you're resource-constrained.
- Alert fatigue. If your detection generates more noise than signal, your team will tune it out. Be ruthless about reducing false positives, even if it means accepting slightly narrower coverage.
- Scope creep. Start with insider threat detection for your most critical systems. Don't try to monitor everything at once or expand into adjacent security domains before you've validated the basics work.
- Neglecting user trust. Your employees should know monitoring exists and understand it's about protection, not surveillance. Transparency prevents the program from becoming a trust issue that damages culture.
- Tool complexity. If a tool requires extensive training, ongoing maintenance, or dedicated resources to operate, it's not built for lean teams. Choose tools that work with minimal overhead or you'll end up abandoning them.
How Presence Simplifies This
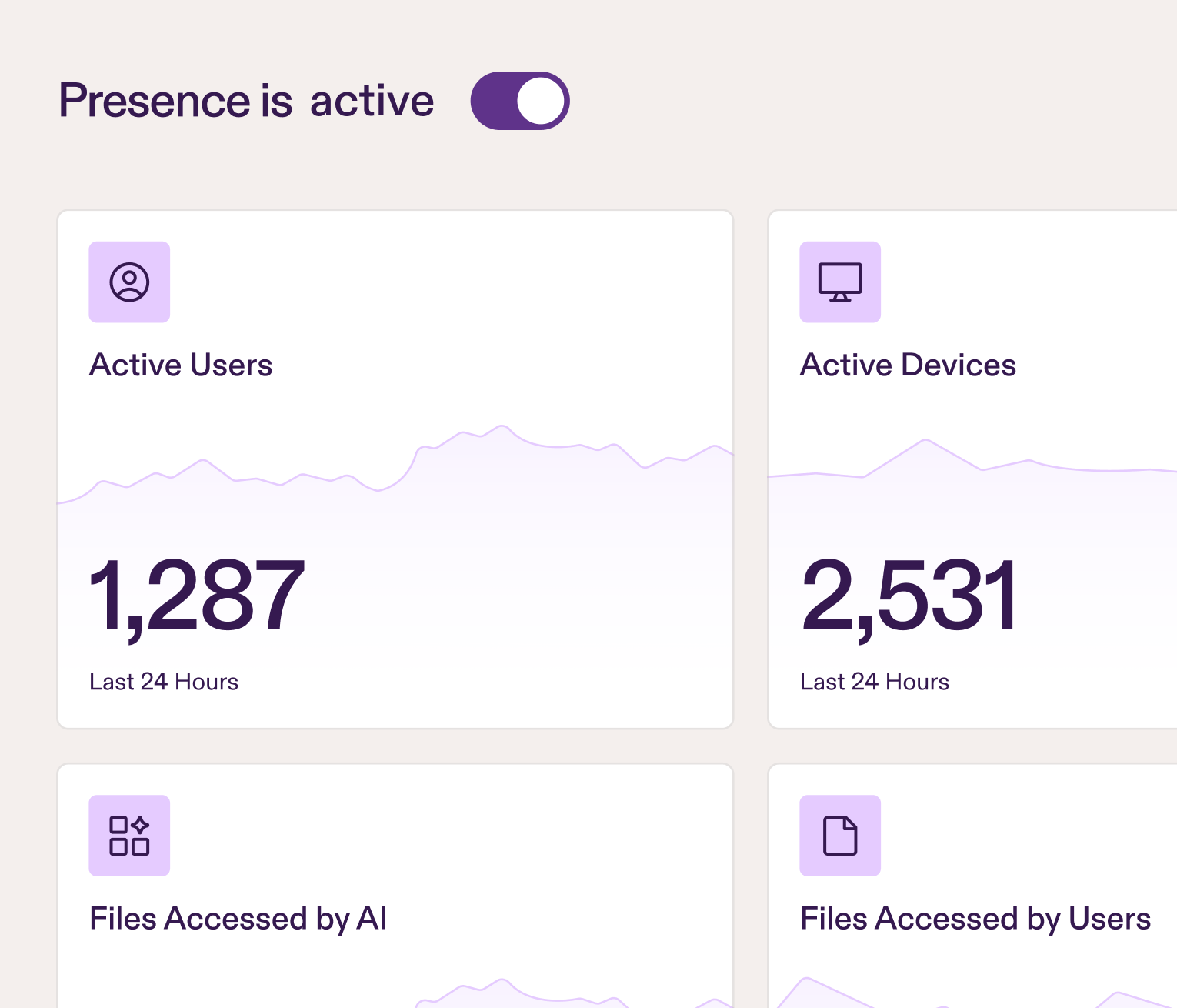
Presence is designed specifically for organizations building insider threat detection without a SOC. It connects to your Microsoft Entra ID in under 10 minutes and immediately begins learning your environment. Behavioral AI baselines normal activity for each user, so anomalies surface automatically without writing rules or tuning thresholds. Canaries protect admin accounts by catching compromised credentials the moment they're misused. Low-risk event tracking highlights smaller security gaps before they escalate. Alerts include full context about what happened and why it's unusual, so you can investigate and respond without needing analyst expertise.
The system adapts as your organization changes, eliminating the maintenance burden that kills traditional detection programs. You get visibility into insider risk without adding headcount or complexity.
See how Presence detects these scenarios in real-time. Email contact@pistachioapp.com to book a 15-minute demo and we'll walk through exactly how it works in your environment.