What are you
interested in?
Category
All
Tags
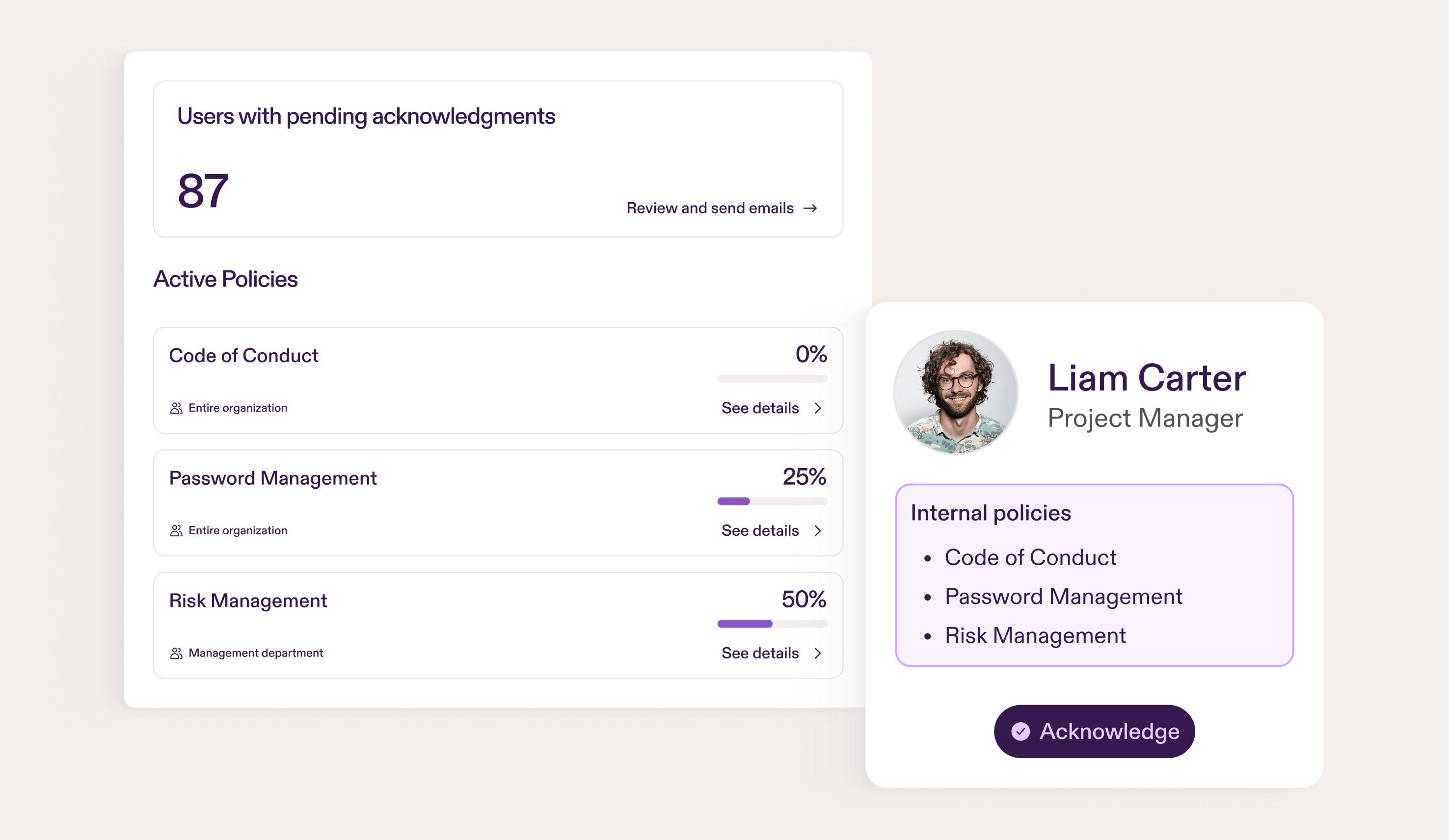
New Feature: Internal Policies
The Hidden Cost of Managing Manual Security Awareness Training Programs

Why Annual Security Awareness Training Doesn't Work (And What Does)

Why Non-Enterprise Companies Are Getting Hit Harder by Phishing

Phishing Risk: The Cost of Inaction
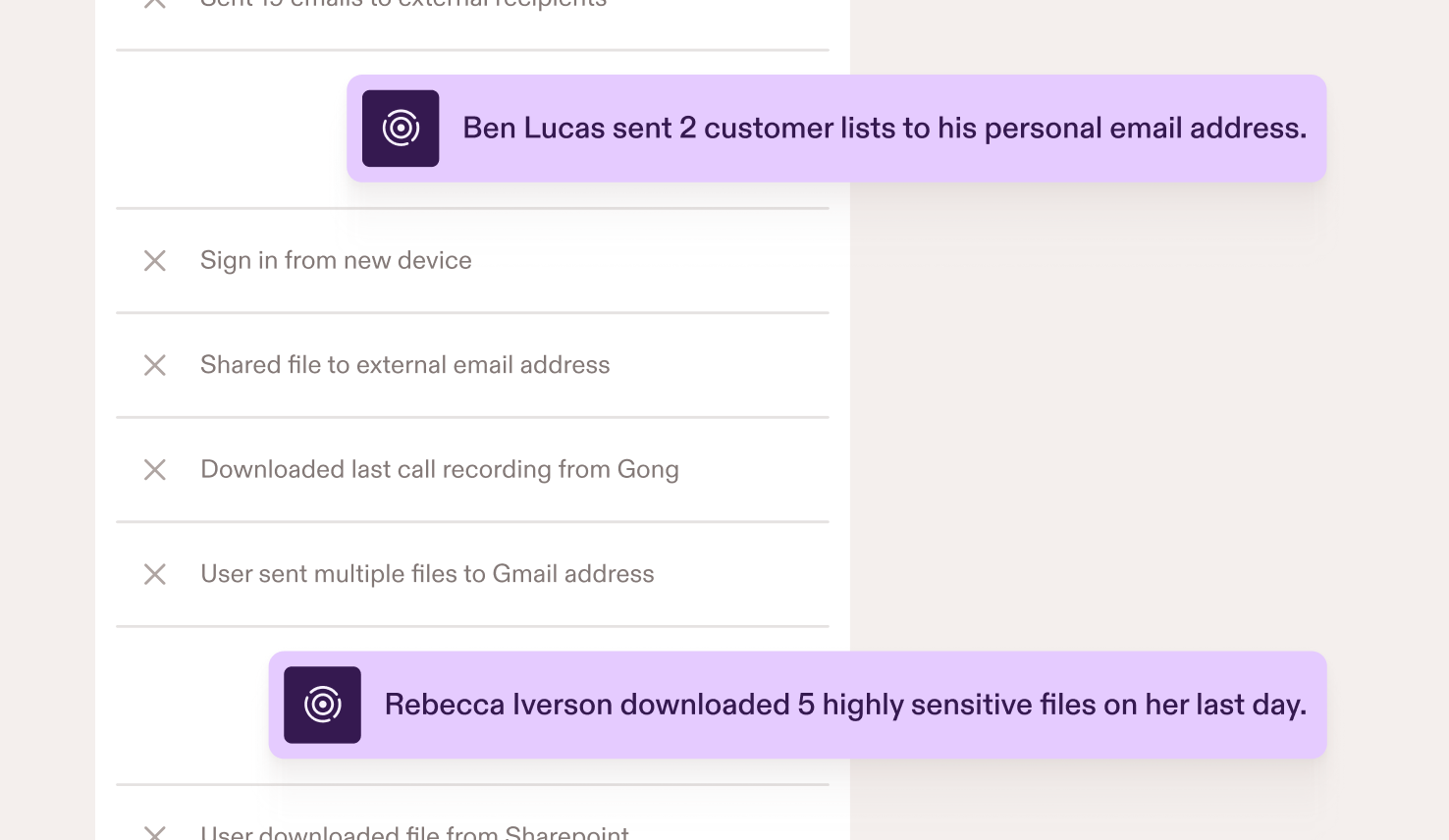
Building an Insider Threat Program Without a SOC
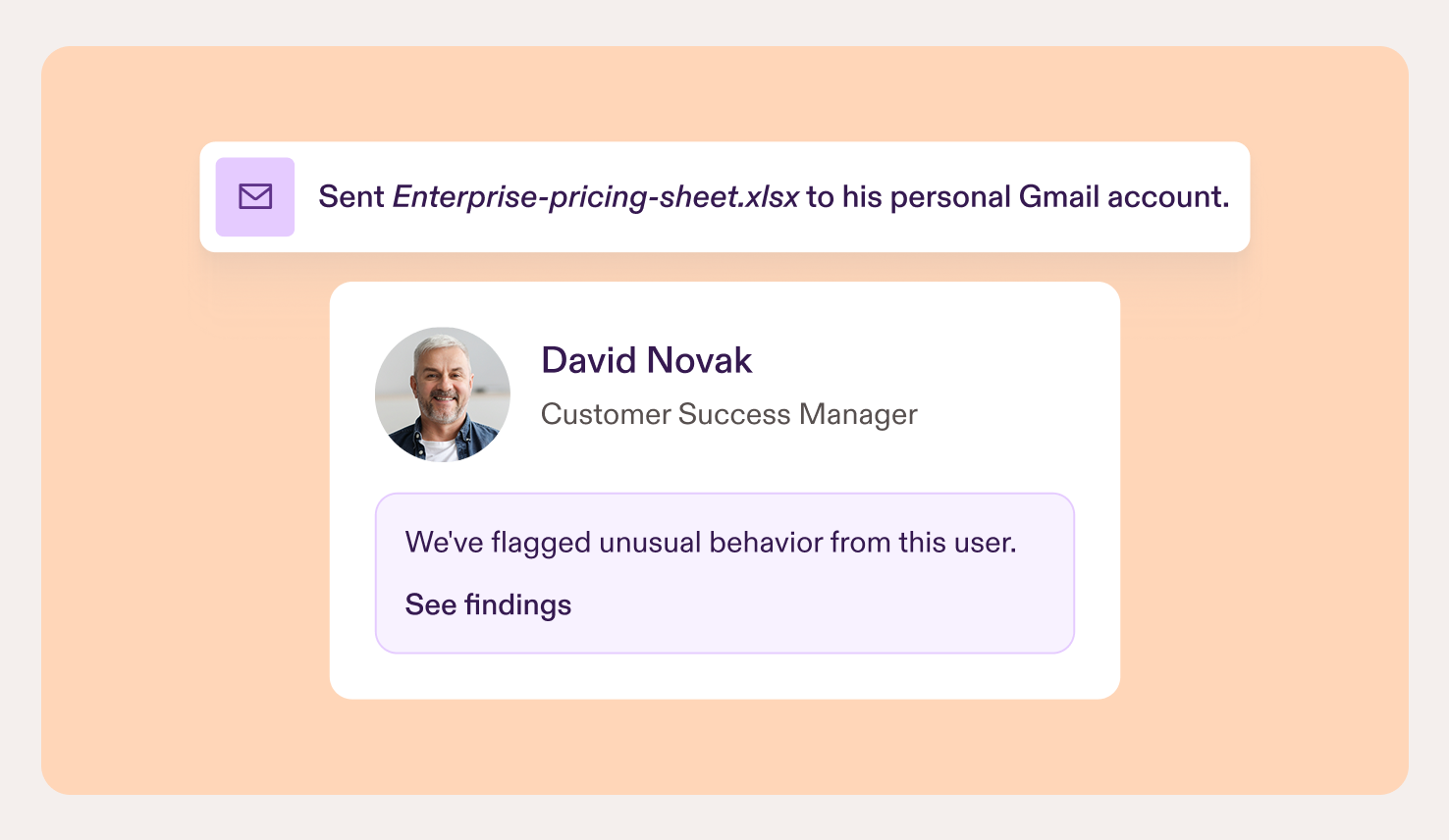
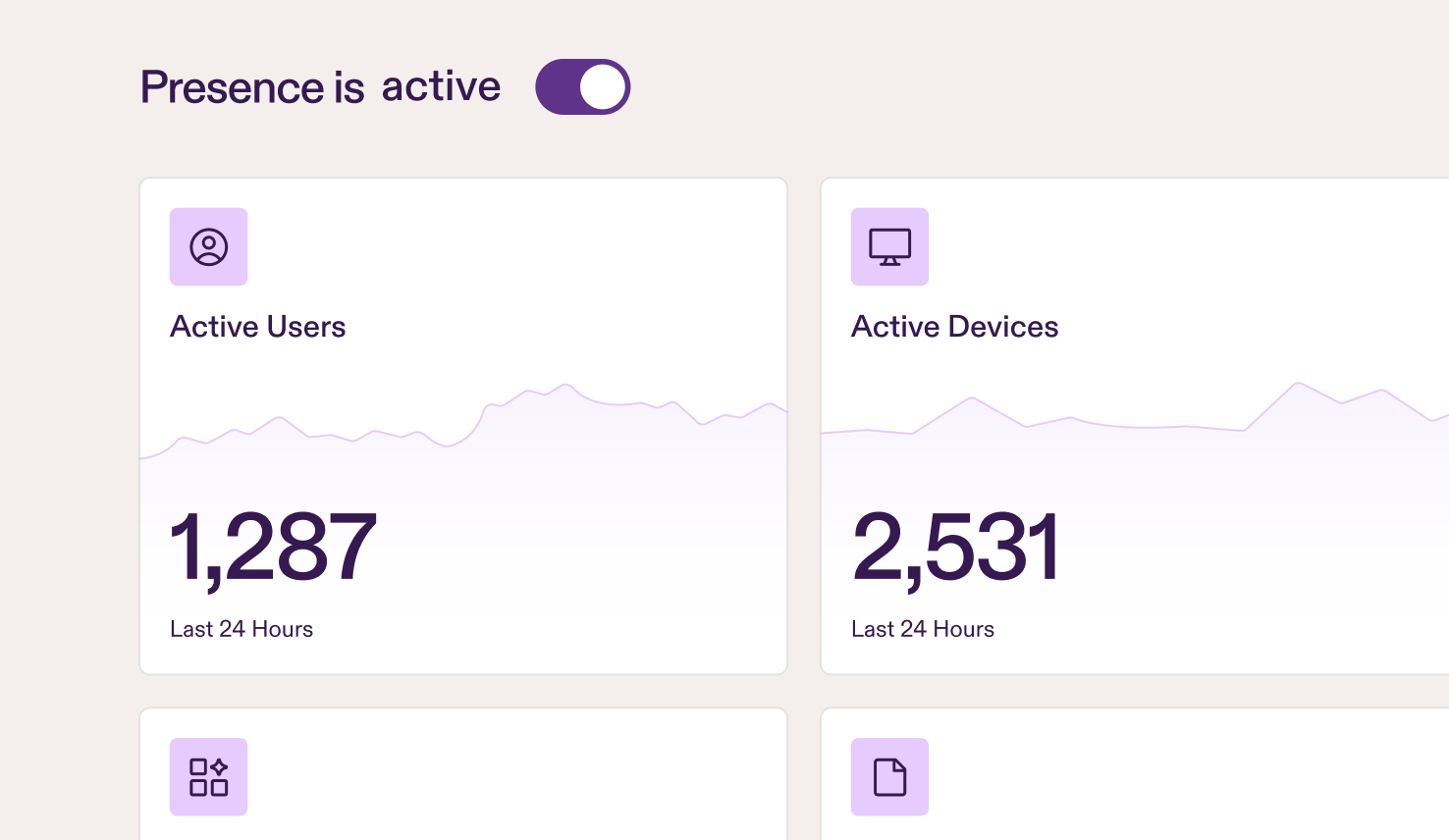
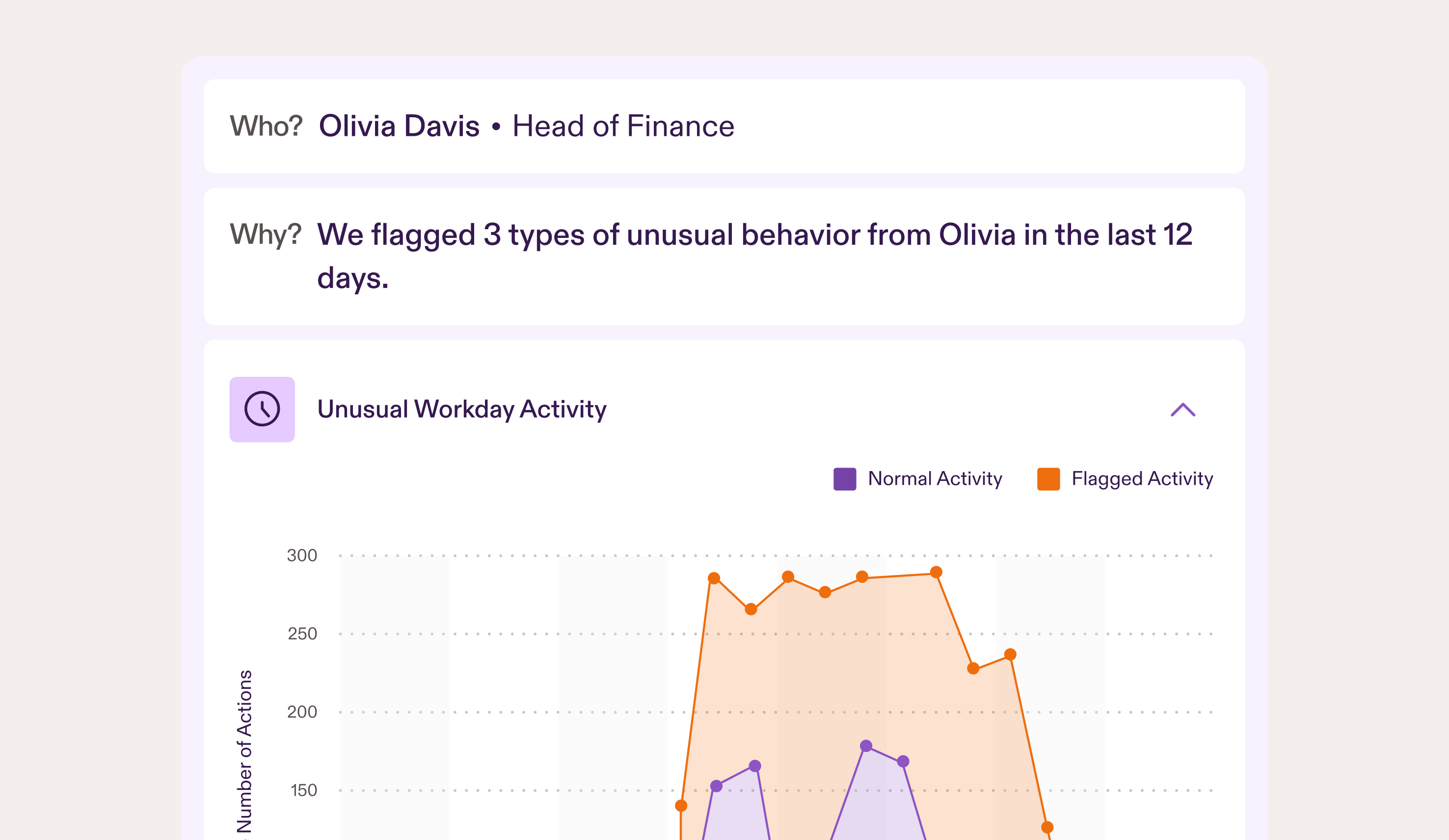
Behavioral Baselines: How AI Learns What Normal Looks Like
What is Insider Threat Detection? (And Why It's Not Surveillance)

Protecting IP During High-Growth: Why Scaling SaaS Companies Can't Ignore Insider Risk
Insider Threat Scenarios You Can't Afford to Ignore
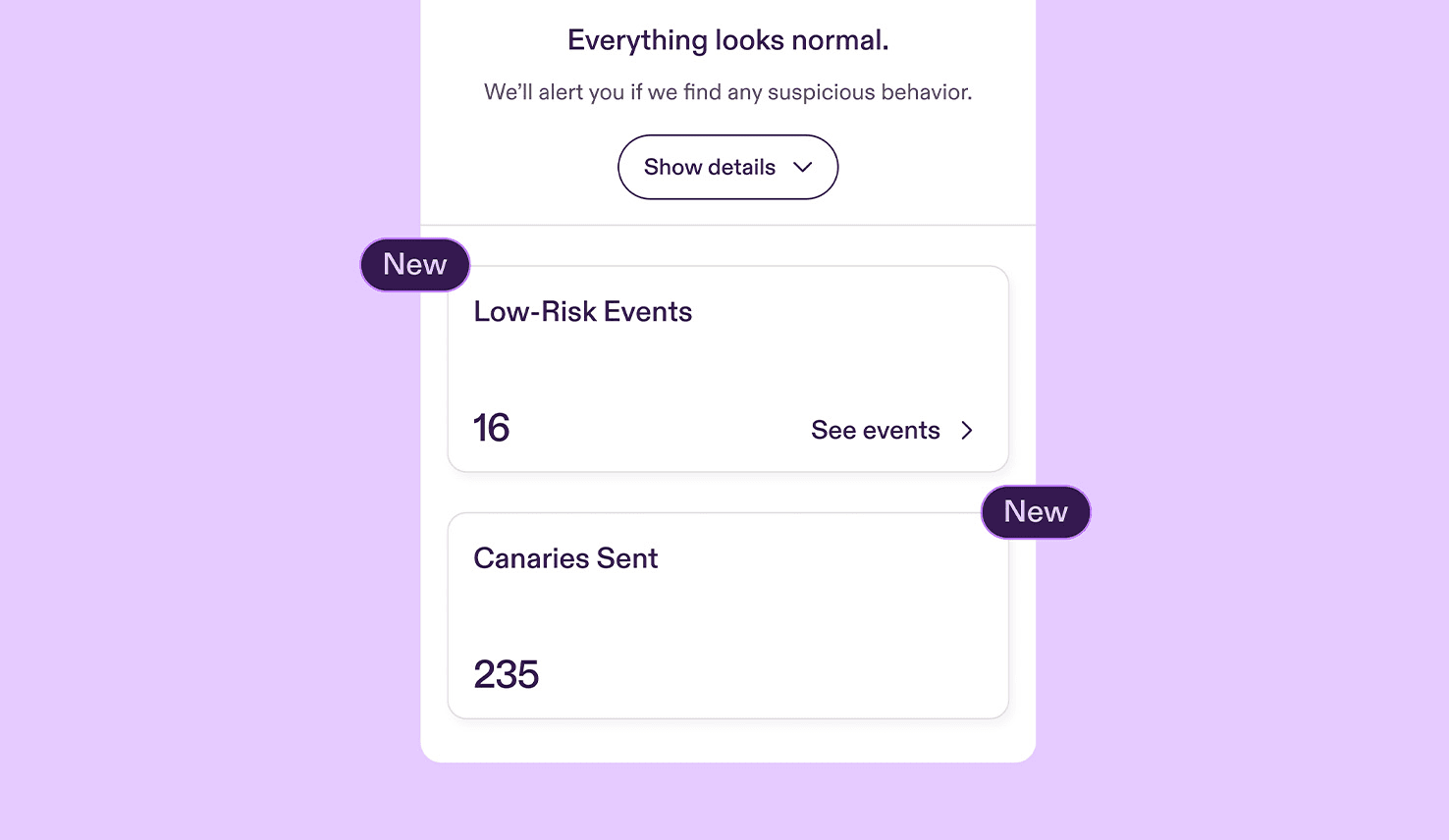
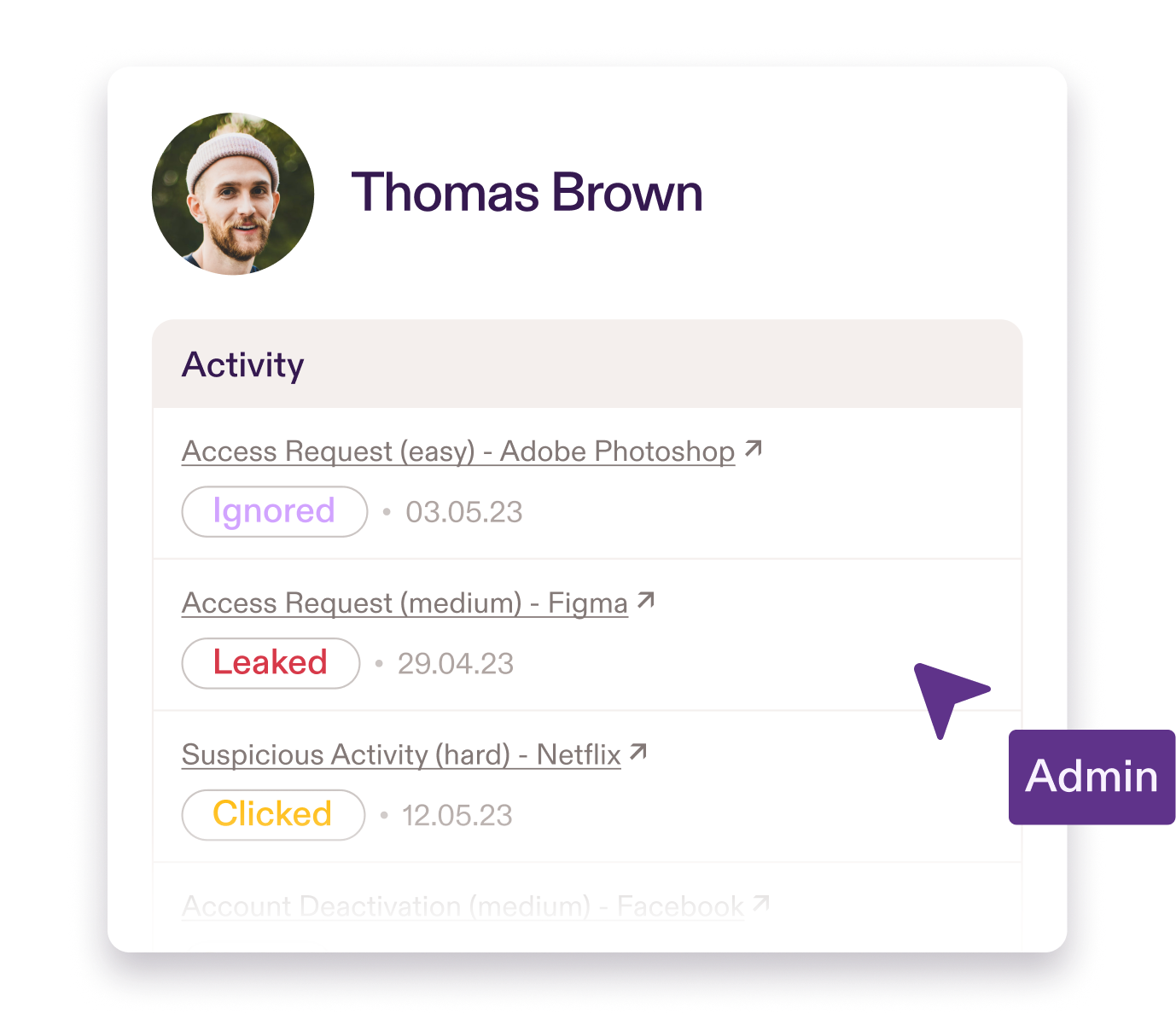
New Features: Canaries and Low-Risk Events
You, Me, and Data Denormalization
Written by Kasper Rynning-Tønnesen
We believe in a learn-by-doing approach over snooze-worthy videos.
Instead, Pistachio tailors real-world scenarios so your team can build their cyber skills in a safe environment.