Ask most IT managers how their security awareness training is going and you will get the same answer: completion rates are fine, but no one is taking the information in. Employees click through the modules. They pass the tests. And then, six months later, someone clicks a phishing link.
They had the training. But they were still breached. And the reason is not that employees are careless - it is that most security awareness training is not designed to build real resilience. It is designed to tick a box.
The Problem with Generic Templates
Most phishing simulation platforms work from a library of pre-built templates. An administrator picks one, schedules a send, and waits to see who clicks. It’s efficient. But it also doesn’t work.
Employees spot patterns. After a few rounds of simulations, they start to notice things: the slightly unfamiliar sender format, the subject lines that tend to arrive on certain days, the visual style that looks almost-but-not-quite like a real Microsoft email. They speak to colleagues, and warn each other. They are not becoming more secure. They are becoming better at spotting your training exercises.
This is a well-documented problem in security. When training is predictable, it produces the same outcome - employees who can pass your test, but are not prepared for the real thing.
Real phishing attacks do not come from a shared template library. They are personalised, timely, and increasingly sophisticated. A finance manager receives an urgent payment request that references a real supplier. A warehouse operative gets a Teams message that looks like it came from their line manager. These attacks work because they do not look like training.
Frequency Matters More Than Most Teams Can Manage
The USENIX SOUPS research on phishing awareness[1] found that employees retained strong detection skills four months after training, but performance declined significantly by six months without reinforcement. Annual training does not come close to bridging that gap. Neither does quarterly, for most organisations.
The frequency problem compounds the template problem. Not only is the content generic, it’s infrequent - which means whatever pattern recognition employees do develop fades before the next simulation arrives.
For IT managers running training manually, there is no good answer to this. More frequent campaigns mean more admin. Better, more realistic simulations mean more time spent building them. The workload does not scale, so the training does not improve.
The result is a program that looks functional on paper - completion rates reported, simulations sent, boxes ticked - but is not meaningfully reducing human risk.
What Good Security Awareness Training Looks Like
Effective security awareness training has a few things in common that generic programs consistently lack:
Continuous: Awareness that fades between annual sessions is not awareness. Training needs to be present enough in employees' working lives that the habits it builds become automatic, not recalled under pressure.
Personalised: A receptionist and a finance director face different threats. A simulation that references tools neither of them uses is not realistic to either of them. Effective training reflects the actual working environment of the person receiving it.
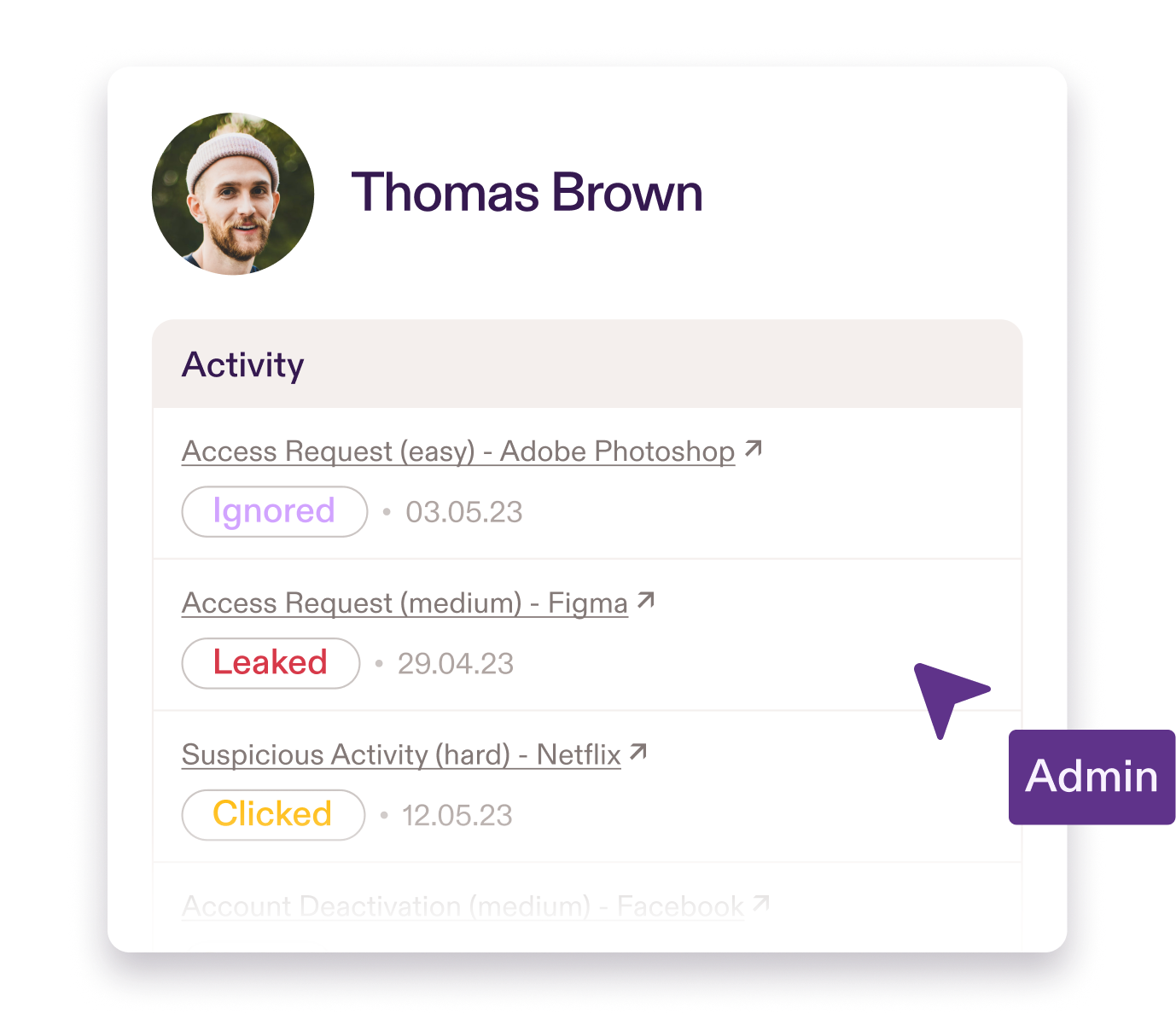
Adaptive: It adapts to individual performance. Employees who consistently identify threats correctly do not need the same training as employees who are still clicking. A one-size program wastes time for some and under-challenges others.
Feedback: When an employee interacts with a simulation, what happens next matters as much as the simulation itself. Instant, contextual feedback - this is why this looked real, this is what to look for next time - is what converts a mistake into learning. A completion rate with no feedback loop is just a measurement of who clicked a link.
Joseph Cunningham, Head of IT Security and Support at OOONO, put it plainly:
"Traditional phishing training feels like a box-ticking exercise, but Pistachio builds real skills over time. My users enjoy the tests, get instant feedback, and even brag about spotting fake emails. I can see a clear improvement in awareness and vigilance that lasts all year, not just after a one-off training session."
That last line is the one worth focusing on: resilience that lasts all year, not just after a training session. That is the difference between a program that runs and a program that works.
The Shift from Compliance to Resilience
There is nothing wrong with wanting to satisfy a compliance requirement. ISO 27001, NIS2, and Cyber Essentials all demand evidence of ongoing security training and meeting those requirements matters. But compliance and resilience are not the same thing, and optimising purely for the former tends to undermine the latter.
A training program built around completion metrics will produce high completion metrics. It will not necessarily produce employees who are harder to phish. The distinction matters because compliance documentation does not stop breaches - informed, alert employees do.
The organisations that get this right tend to stop thinking about training as a program to administer and start thinking about it as a culture to build. Security awareness becomes something employees encounter regularly, in context, in a way that feels relevant rather than mandatory. The goal shifts from "everyone has done the training" to "everyone is getting better at spotting real threats."
How Practice Approaches This Differently
Practice was built around the gap between these two outcomes.
Simulations run continuously and are personalised to each employee's role and the specific tools they use - not built from a generic template library. They adapt based on individual performance, so each person is being challenged at the right level rather than receiving the same simulation as everyone else. Multi-channel delivery across email and Microsoft Teams, reflects the actual attack surface employees face, not just the most convenient format to simulate.
When an employee interacts with a simulation - whether they spot it or not - they receive immediate, contextual feedback. That feedback is the training. The simulation is just the trigger.
The result is awareness that compounds over time rather than resetting with each annual session. Employees who are not just better at completing modules, but genuinely harder to deceive.
Moving Away From Generic Training
Generic training teaches employees to recognise your simulations. It does not teach them to recognise real attacks.
The fix is not running more of the same training more often. It is training that is realistic enough, frequent enough, and personalised enough to build habits that hold up when a genuine threat arrives.
Practice delivers continuous, adaptive, role-based simulations that build real resilience - without adding to your workload.
See how Practice builds lasting resilience. Email contact@pistachioapp.com to book your 15-minute demo.