Building internal resilience to phishing attacks is no longer optional. It is now a baseline requirement for any organisation serious about continuity, compliance, and trust.
Most reliable entry point for ransomware, invoice fraud, and credential theft. It is not a niche technical problem. It is an enterprise risk that escalates quickly, generating financial, operational, and regulatory exposure that touches customers, profitability, and brand reputation in equal measure.
And yet, most organisations are still approaching it the same way they did a decade ago: an annual training exercise, a tick in the compliance column, and the quiet hope that employees will simply know better than to click.
Why It Matters Now
The threat landscape has changed, and AI is accelerating it. Phishing attacks have grown in volume, sophistication, and consequence. They are no longer crude mass-spam operations. AI allows attackers to generate convincing, personalised messages at scale, scraping LinkedIn and company websites to reference a target's role, colleagues, and recent activity. The "bad English" heuristic that many people were trained to spot is largely obsolete.
Voice and video cloning have made the problem worse. There are documented cases of finance teams transferring large sums after receiving what appeared to be a video call from their CFO[1]. Attackers can also mirror the writing style of a compromised email account closely enough to fool direct reports and colleagues.
The result is that attacks are harder to detect, easier to launch, and more likely to succeed. The downstream effects of a single successful click now include financial loss through fraud, ransomware payments, and payment diversion; operational disruption from system lockouts and extended downtime; reputational damage through customer attrition and press coverage; and regulatory exposure through mandatory breach reporting and personal liability for directors.
The Scale of the Problem
The numbers are not abstract. Phishing is the dominant vector for virtually all serious cyberattacks. Ninety-four percent of malware is delivered via email[2]. Ninety-one percent of successful cyberattacks begin with phishing[3]. Business email compromise has increased by more than 40 percent in the last 24 months[4].
The financial consequences follow. Mid-market firms report an average loss of USD 11 million per cyber incident[5]. For smaller businesses, the average breach cost sits around USD 1.2 million, a figure that, combined with 8 or more hours of downtime per attack, can prove existential[6]. Fifty-eight percent of SMBs have experienced downtime due to a cyberattack[7], and 60 percent shut down within six months of a major inciden[8].
A Global Problem, Felt Locally
The impact is not theoretical. In 2024, approximately 3,500 targeted phishing attacks were recorded against Nordic enterprises[9]. In the first half of 2025, UK organisations reported £629.3 million in fraud losses across 2.09 million cases, a 17 percent year-on-year rise driven heavily by social engineering-enabled scams[10]. In Germany, cybercrime losses reached €267 billion in 2025, with phishing and identity-related fraud identified as major contributors across sectors[11].
These are not fringe incidents involving poorly resourced organisations. They are happening to established enterprises, public sector bodies, and financial institutions with security teams, policies, and tools already in place.
The Regulatory Dimension
The compliance landscape is tightening. Security governance frameworks now explicitly require senior management to demonstrate active oversight of phishing risks, not just awareness of them.
ISO 27001 requires top management to conduct risk assessments addressing phishing and implement "appropriate" awareness training, language that specifically excludes generic annual exercises. Under NIS2 in the EU, directors of essential entities face personal liability for inadequate security measures, bringing human risk squarely into scope for board-level accountability. Across all markets, contractual obligations, insurance requirements, and director duties create personal exposure when management cannot demonstrate due diligence.
In an audit, investigation, or courtroom, "we did a yearly training" is no longer sufficient.
Why Standard Training Is Not Enough
System controls cannot fully prevent employees from clicking links or sharing credentials. Firewalls, email filters, and endpoint protection all have a role, but none of them address human behaviour directly.
Most organisations rely on annual training that creates awareness but not behaviour change. Employees who completed a module in January are largely indistinguishable, in terms of actual risk, from those who did not. The knowledge fades. The habits do not form. The exposure remains.
Measurable resilience requires something different: realistic, repeated simulation, targeted coaching, and visible progress over time.
The Investment Case
Phishing incidents are frequent and expensive. A programme that costs a fraction of a million-dollar breach and meaningfully reduces the probability of an incident is not a discretionary spend. It is a business continuity control.
Budget holders who continue to treat phishing resilience as an awareness exercise are accepting a level of exposure that is increasingly difficult to justify to boards, auditors, insurers, and customers.
How Pistachio Helps
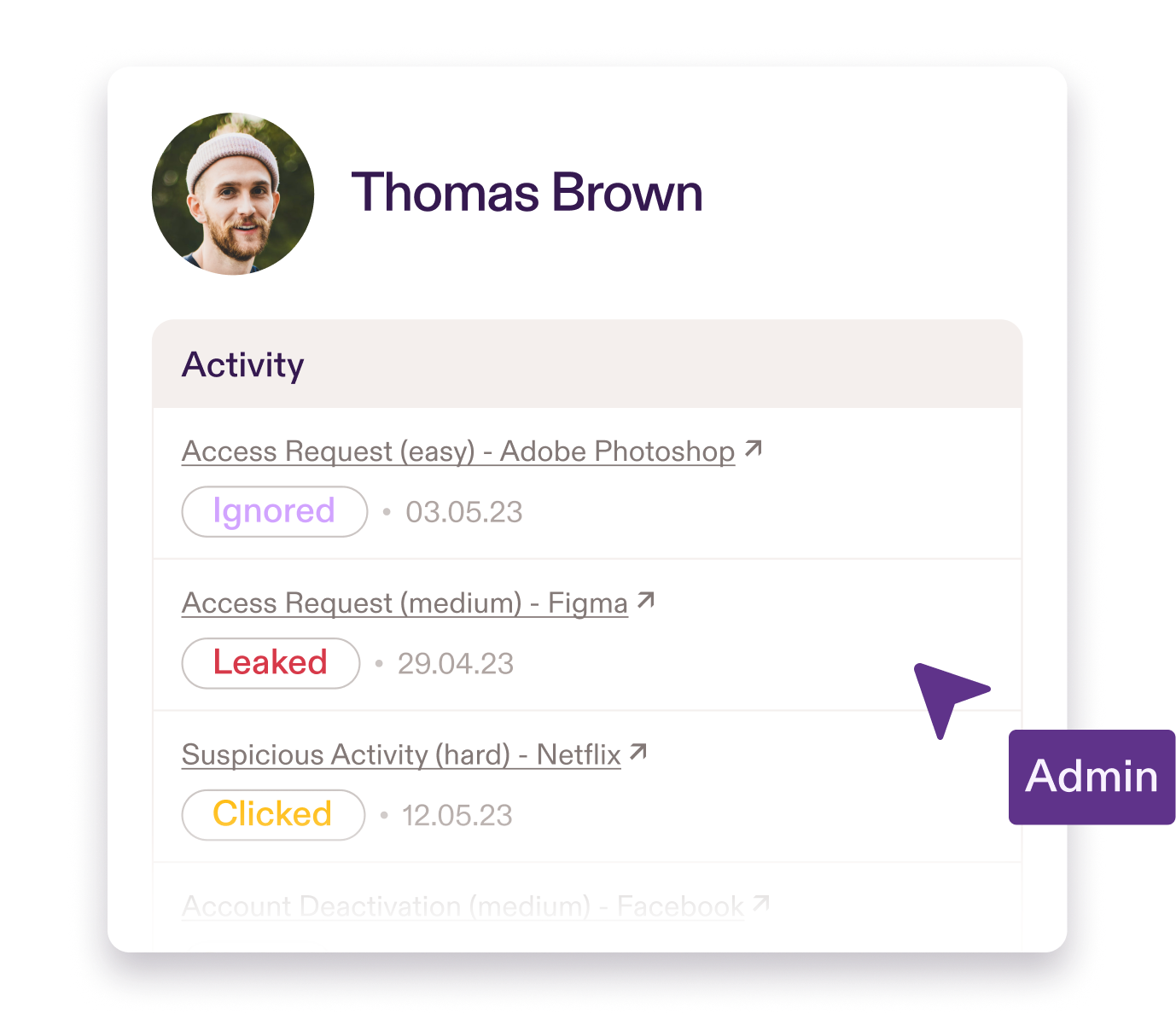
Pistachio Practice is a security awareness training platform that combines realistic phishing simulations with personalised training. Simulations run automatically, mapped to employee roles, identifying high-exposure teams and measuring risk reduction over time. Personalised training reinforces this through short scenario-based exercises delivered directly to employees via Outlook or Slack, covering everything from brand spoofing and smishing to physical security and AI prompt injection.
One customer reduced their phishing click rates from 20 to 25 percent down to 1 to 2 percent. That is the difference between basic awareness and measurable resilience, and it is a practical investment that reduces financial, operational, and reputational exposure across the organisation.
The impact is not theoretical. In 2024, approximately 3,500 targeted phishing attacks were recorded against Nordic enterprises. In the first half of 2025, UK organisations reported £629.3 million in fraud losses across 2.09 million cases, a 17 percent year-on-year rise driven heavily by social engineering-enabled scams . In Germany, cybercrime losses reached €267 billion in 2025, with phishing and identity-related fraud identified as major contributors across sectors.