If you manage IT for a company with 50 to 500 employees, your security awareness training program probably looks something like this: a spreadsheet tracking who has completed what, a calendar reminder to schedule the next phishing simulation, a quarterly scramble to pull compliance reports before an audit, and a steady stream of follow-up emails chasing the 30% of staff who still haven't finished last month's module.
You need to do it. But it’s taking up too much of your time.
And to make matters worse: all that effort - the scheduling, the chasing, the report-pulling - is not producing the outcome it is supposed to. Employees are not becoming meaningfully more resilient. The admin burden is real, and the training is not working anyway.
The conversation about security awareness training tends to focus on one of those problems at a time – but they’re connected.
The Admin Overhead Nobody Accounts For
When organizations buy security awareness training, they budget for the license. They rarely budget for the internal time required to make it run. That time is harder to see on a spreadsheet, but it is very easy to feel.
Where is the time spent?
Campaign scheduling: Most training platforms require an administrator to build and launch phishing simulations manually. That means choosing templates, configuring target groups, setting send windows, reviewing results, and then doing it again next month. If you want simulations that feel realistic and are not immediately flagged as training exercises, you need to invest time keeping them current.
Chasing completion: A 70% completion rate is often cited as a baseline target for security training programs. Getting there manually means identifying who has not completed training, sending reminders, escalating to managers, and logging exceptions. For an organization with 200 employees, hitting that threshold every cycle is a part-time job.
Compiling audit reports: When a customer security questionnaire arrives, or when an auditor asks for evidence of your ISO 27001 or NIS2 compliance program, someone must pull that data together. If your training platform does not produce ready-made compliance reports, that someone is you, working from exports, spreadsheets, and memory.
Policy management: Acceptable use policies, data handling policies, information security policies - most organizations track acknowledgement in a spreadsheet or a shared folder. When an employee joins, someone sends the documents. When the policy updates, someone chases signatures. When an auditor asks for evidence, someone reconstructs the paper trail.
Why This Problem Is Worse at SMBs
Enterprise organizations have dedicated security teams. They have security operations analysts, compliance managers, and GRC tools built specifically to automate this work. The overhead still exists, but it is distributed across enough people that no single person feels the full weight of it.
At a company with 100 to 500 employees, the IT team is typically one to five people covering everything: endpoints, identity, SaaS, network, helpdesk, and security. According to Devolutions' 2025 State of IT Security in SMBs report[1], only 22% of SMBs say they have an advanced security posture - despite 71% saying they feel confident about handling a major incident. That gap between confidence and actual readiness is not unusual. It is what happens when teams are managing security reactively, fitting it in around everything else.
Security awareness training is not exempt from that squeeze. It competes directly with patching, onboarding, vendor management, and ticket resolution. When something must give, it is usually the proactive work - the stuff that matters most for resilience but does not trigger an immediate incident if it slips.
The result is training programs that run inconsistently, simulations that launch months apart, completion rates that drift, and compliance documentation that is always slightly out of date. But there is a second consequence that is less obvious and more damaging: when admin burden consumes all available capacity, the quality of the training itself often suffers.
When Admin Pressure Impacts Training Quality
There is a meaningful difference between a training program that runs and a training program that works. Most stretched IT teams end up with the former.
When managing the program becomes the primary goal, the metric that gets optimised is completion rate, not behaviour change. Chasing 70% becomes the objective. Whether those 70% are learning anything is a harder question, and there is rarely time to ask it.
The science on this is clear. A study presented at the USENIX SOUPS security conference[2] found that employees could accurately identify phishing attempts four months after training, but performance declined significantly after six months without reinforcement. Annual or biannual training does not maintain the level of awareness needed to catch real attacks - and for most stretched IT teams, that is precisely the cadence they are stuck with.
There is also the problem of generic content. When simulations are built manually from a fixed template library, employees quickly learn to recognise them. They start looking for the tells: the slightly off sender name, the familiar visual style, the subject lines that always seem to arrive on a Monday. That pattern recognition is not resilience. It is employees getting good at spotting your training exercises, not real phishing attempts. When a genuinely novel attack lands in their inbox, the training offers no protection.
The practical consequence is that stretched IT teams end up investing significant time into a program that satisfies a compliance checkbox but does not move the needle on actual risk. The hours go in. But behaviour does not change. That is not a reflection of poor IT management - it is the result of asking one person to do work that requires continuous, personalised, adaptive delivery at scale.
The Compliance Pressure Is Only Increasing
The administrative burden of security awareness training is getting harder to ignore, because regulatory expectations are getting harder to meet.
NIS2, which came into effect across EU member states in October 2024, explicitly requires organisations to implement security awareness training as part of their risk management measures. ISO 27001 has long required evidence of ongoing security education. Cyber Essentials, which many UK businesses pursue to satisfy cyber insurance or contract requirements, expects documented training practices.
These frameworks do not just require training to exist. They require evidence that it is happening, consistently, across the organisation. That evidence needs to be producible on request, not reconstructed under audit pressure.
For IT teams already stretched thin, that documentation requirement adds another layer to an already heavy workload. The scale of the problem is reflected in how organisations are responding: according to compliance operations research published via ISACA[3], the share of organisations using automation tools to manage compliance preparation jumped from 25% to 72% in a single year - driven largely by the volume of manual work involved in staying audit-ready without dedicated compliance staff.
The Double Problem: Paying Full Price for Half the Outcome
Put it together and we've got a double-sided problem. Manual security awareness training programs require time IT teams don't have available. This results in substandard training - which is infrequent, generic, and optimised for completion rather than behaviour change - so the organisation does not get the risk reduction it needs.
You are spending time you do not have on a program that is not working as well as it should be.
That is the real hidden cost. It is not just the hours. It is the hours plus the gap between what the training is supposed to achieve and what it is delivering.
What "Zero Maintenance" Actually Means in Practice
Anthony Balfour, IT Security Specialist at Lhoist Group, described exactly this situation before switching to Pistachio’s Practice platform:
"In the beginning, we relied on a platform that required extensive configuration and manual effort, selecting and crafting phishing campaigns every month for users globally. Pistachio has reduced our manual workload to zero with its automated phishing simulations and in-box delivery of scenario-based trainings. This has allowed our team to dedicate time to other important security initiatives while Pistachio handles our Security Awareness program seamlessly."
When IT managers describe their current training setup, a phrase that comes up repeatedly is: "I'm constantly chasing to hit 70 percent." Not building resilience. Not improving quality. Just chasing a number.
The alternative is not a program that requires less administration. It is a program where the administration does not exist, and the quality problem is solved at the same time.
That is what Practice was built to do.
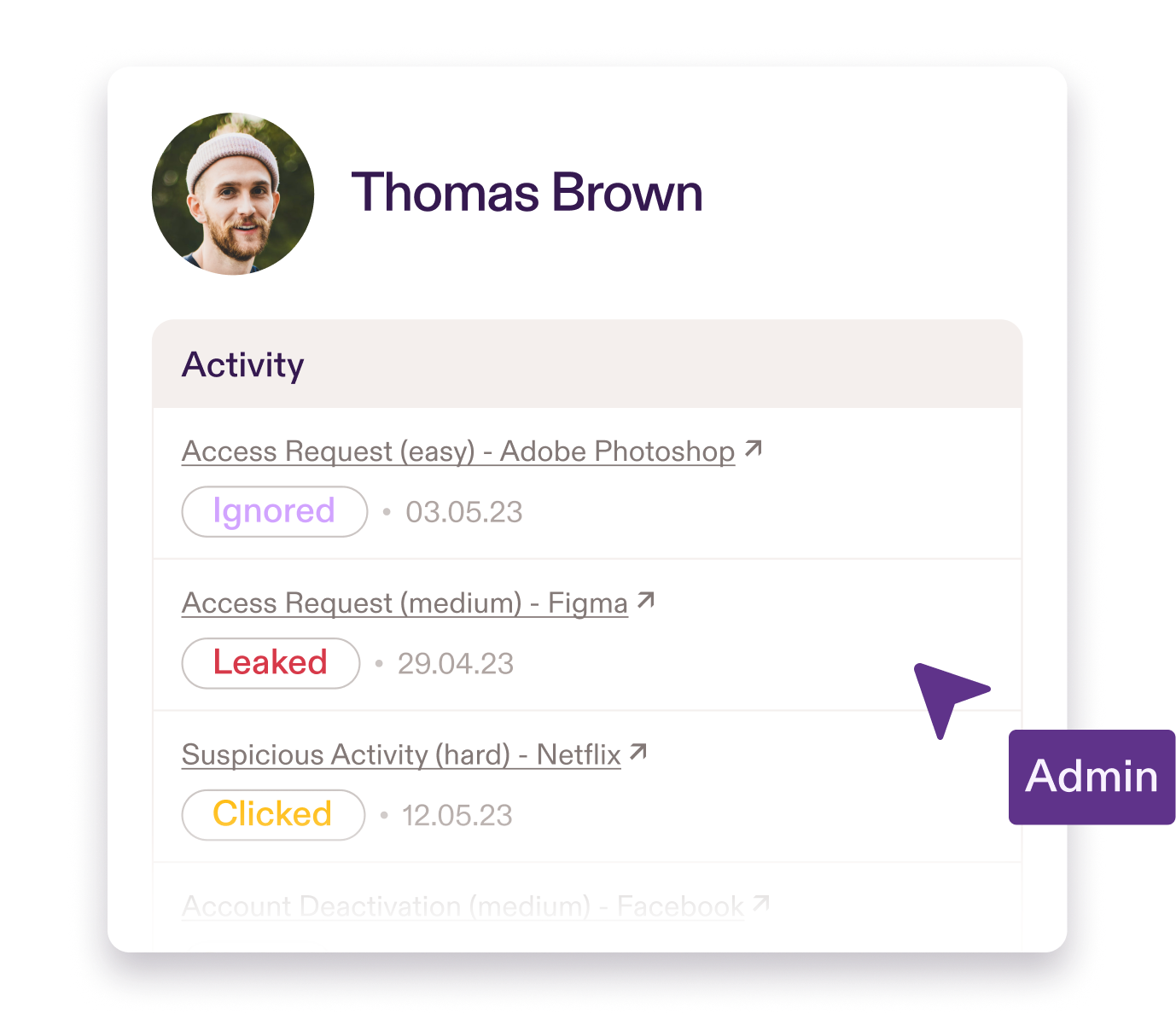
Practice deploys in ten minutes by syncing with Microsoft Entra ID. It automatically enrols new employees when they join and removes access when they leave. From that point, it runs without input. Phishing simulations go out continuously across email and Microsoft Teams. They are personalised to each employee's role and the specific tools they use - realistic enough that employees cannot pattern-match their way past them. Simulations adapt based on individual performance over time, which means each person is being trained at the right level of difficulty, not on a one-size schedule that treats a finance director the same as a warehouse operative.
That continuous, adaptive delivery is not just more convenient than manual campaigns. It is meaningfully better training. Spaced, role-relevant, realistic simulations build the kind of genuine behavioural resilience that infrequent generic exercises cannot.
Reporting is automated. When you need to demonstrate compliance with ISO 27001, NIS2, or Cyber Essentials, the data is already there, structured and ready to share. Policy management works the same way - distribution, acknowledgement tracking, and audit trails handled automatically.
The result is a training program that maintains itself, improves itself, and documents itself. You see the output - phishing resilience scores, risk trends, compliance status - without doing the underlying work to produce it. And crucially, the output reflects something real: employees who are better at identifying threats, not just better at completing modules.
Quantifying the Return
If your current training program is taking ten hours a month to manage, and your fully loaded IT labour cost is €55 to €90 per hour, that is €550 to €900 in internal labour costs every month, before accounting for the opportunity cost of everything else that did not get done.
Over a year, that is between €6,600 and €10,800 in IT time spent on training administration alone.
An automated platform does not just reduce that cost. It reallocates that capacity to work that moves the needle, while simultaneously running a training program that is more frequent, more personalised, and more effective than what a stretched team can produce manually.
Moving Away From Manual Security Programs
The hidden cost of managing security awareness training programs is not just the hours. It is the hours spent on work that produces worse outcomes than an automated system would deliver without any input at all.
For lean IT teams, it’s hard to ignore: manual training management is expensive, and the training is not as good as it could be. Automation solves both problems at once.
Practice removes the admin burden and runs better training than a stretched team can manage manually. Ten-minute setup. Automated simulations. Adaptive, role-based personalisation. Automated reporting. Zero ongoing maintenance.
See how Practice builds lasting resilience. Email contact@pistachioapp.com to book your 15-minute demo.