Let's address the obvious concern first: insider threat detection sounds like workplace surveillance. The phrase alone conjures images of monitoring every keystroke, tracking bathroom breaks, or reading private messages. If that's your mental image, you're not alone. And you're also not wrong to be concerned.
But here's the reality. Effective insider threat detection has nothing to do with surveillance. It's not about tracking productivity, monitoring what employees say, or micromanaging their time. It's about identifying behavior that suggests an account is being misused, whether by a malicious insider, an accidental mistake, or an external attacker using stolen credentials.
The distinction matters. One protects your organization. The other erodes trust and invites legal risk.
What Actually Constitutes an Insider Threat?
An insider threat is any risk to your organization's data, systems, or operations that comes from someone with legitimate access. This breaks down into three categories:
Malicious insiders are people with authorized access who intentionally cause harm. A departing employee who downloads client lists before joining a competitor. A disgruntled team member who deletes critical files. An insider who sells access to external attackers. These incidents are rare, but the damage can be severe.
Compromised accounts are the most common insider threat. An attacker phishes your Head of Finance, gains valid credentials, and begins exploring your environment. To your security tools, everything looks normal because the credentials are real. The account is behaving unusually, but without baseline detection, you'd never know.
Accidental insiders are well-meaning employees who create risk through carelessness or convenience. Emailing sensitive files to personal accounts. Storing passwords in shared documents. Using unsecured file sharing services. No malicious intent, but the exposure is real.
According to the 2024 Ponemon Cost of Insider Threats Global Report, the average cost of an insider threat incident reached $16.2 million. For organizations without dedicated security teams, a single incident can be existential.
Why SMBs and Mid-Market Companies Are Especially Vulnerable
Enterprise organizations have Security Operations Centers, dedicated analysts, and multi-layered detection systems. They can afford to throw resources at the problem.
Most organizations can't. You're running lean. Your IT team is managing infrastructure, handling support tickets, dealing with vendor relationships, and keeping systems operational. Writing detection rules, tuning alerts, and investigating anomalies isn't feasible when you're already stretched thin.
But the threats don't scale down just because your team does. A compromised admin account is just as dangerous at a 200-person company as it is at a 20,000-person enterprise. The difference is you have fewer people to notice and fewer resources to respond.
This is why insider threat detection matters for lean teams. You need visibility without complexity. Protection without adding headcount.
What Insider Threat Detection Actually Monitors
Here's what modern insider threat detection looks at:
Access patterns. Who is accessing which files, systems, and applications? Is someone suddenly browsing directories they've never touched? Are they downloading data they don't normally work with?
Timing and location. When are users logging in? Is your marketing manager connecting at 3 AM from an unfamiliar location? Is an account active during hours that don't match the user's normal schedule?
File activity. Are large volumes of files being downloaded or exported? Is sensitive data being emailed to external addresses or uploaded to personal cloud storage?
Behavioral anomalies. Is an account doing things that don't match its established pattern? Sudden changes in behavior often signal compromise or intent.
Notice what's missing from that list: email content, chat messages, screen recordings, productivity metrics, or anything related to how well someone is doing their job. Detection focuses on actions that could indicate misuse, not performance or personal activity.
The Privacy-First Approach
Good insider threat detection is designed with privacy as a core principle. You're not reading emails. You're seeing that 50 files were attached to an external email. You're not tracking work hours. You're flagging that an account logged in from a new country at an unusual time.
The goal is to surface risk, not invade privacy. Employees should know monitoring exists, what it covers, and why it's in place. Transparency builds trust. Secrecy destroys it.
This also means detection tools should only alert on credible threats. If your system generates 100 alerts per day and 95 are false positives, you're not building security. You're building alert fatigue and training your team to ignore warnings.
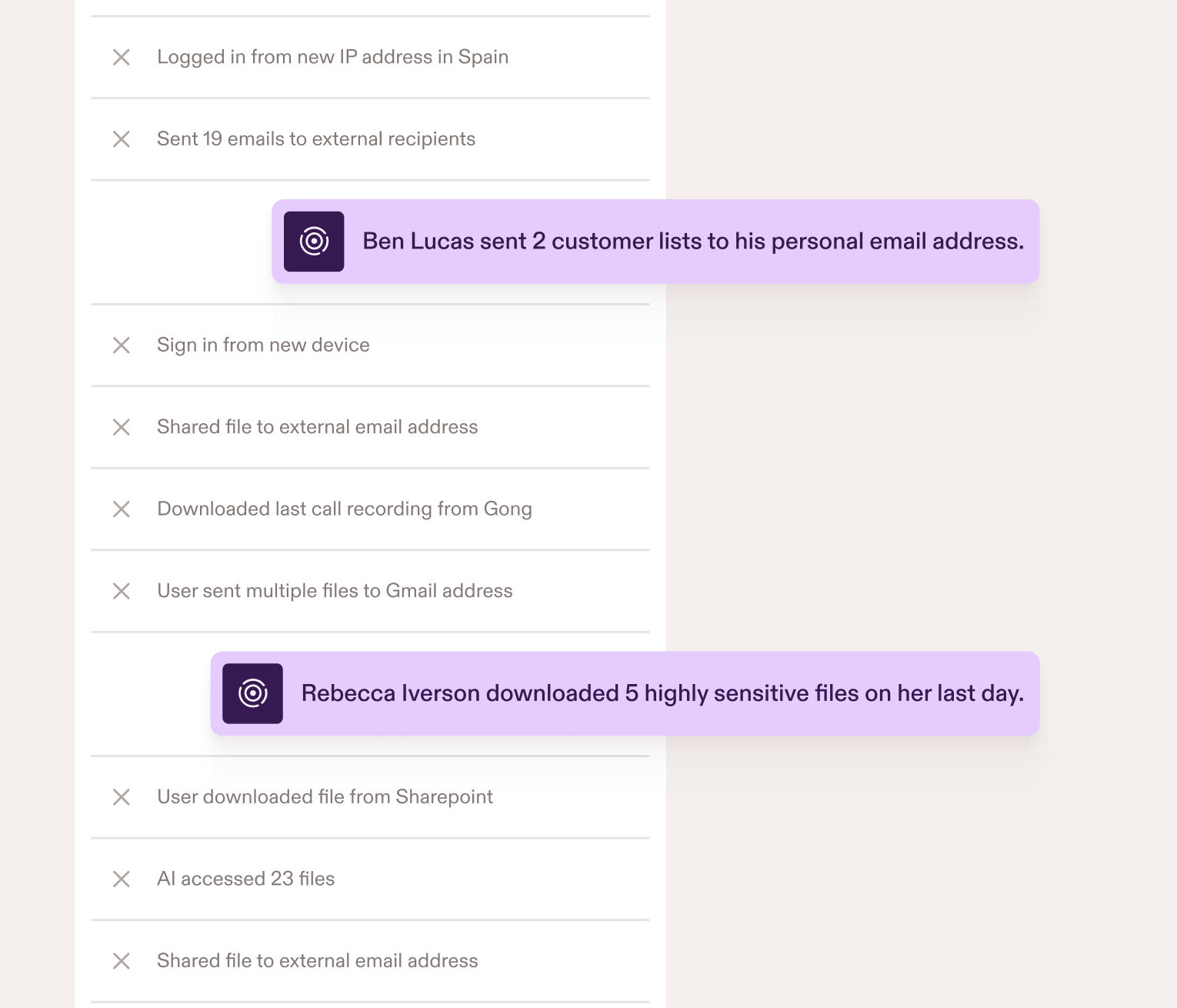
Behavioral AI solves this by learning what normal looks like for each user. Instead of rigid rules that treat everyone the same, it understands context. Your Head of Finance working late during quarter-close isn't suspicious. That same account accessing engineering files at 2 AM is.
Why This Matters Now
The shift to cloud-based work has fundamentally changed the threat landscape. Your data lives in Microsoft 365, HubSpot, and dozens of other SaaS tools. Users access these systems from home offices, coffee shops, and airports. The perimeter is gone.
Traditional security tools were built for a world where data lived on-premises and users worked from corporate networks. They're not equipped to handle distributed access patterns or cloud-native environments.
Insider threats thrive in this environment. A compromised account can access sensitive data from anywhere, at any time, and traditional tools won't notice because the credentials are valid.
You need detection that works where your data actually lives. That means integrating with your cloud environment, understanding how your team actually works, and surfacing threats before damage occurs.
What Good Detection Looks Like for Lean Teams
If you're building insider threat detection without a SOC, you need tools that:
Deploy quickly. Months of setup isn't realistic. You need something that integrates with your existing environment and starts working immediately.
Require minimal tuning. You don't have analysts to write detection rules or investigate endless alerts. Behavioral AI should handle the heavy lifting.
Provide context. Alerts should explain what happened, why it's unusual, and what to do about it. You shouldn't need a background in threat analysis to understand the risk.
Respect privacy. Detection should focus on misuse, not surveillance. Your team should trust that the system exists to protect them, not monitor them.
Moving Forward
Insider threats aren't going away. The longer you operate without detection, the wider the window for unnoticed compromise, data exfiltration, or accidental exposure.
The question isn't whether you need insider threat detection. It's whether you're going to implement it before an incident forces your hand.
Good detection protects your organization without compromising employee privacy. It gives you visibility into risk without adding complexity to your team's workload. And it works for organizations of any size, not just enterprises with dedicated security budgets.
How Presence Delivers Privacy-First Detection
Presence connects to your Microsoft Entra ID in under 10 minutes and immediately begins learning your environment. Behavioral AI baselines what normal looks like for each user, so anomalies surface automatically without writing rules or tuning alerts. Canaries protect admin accounts by alerting you the moment a compromised account takes the bait. Low-risk event tracking highlights everyday actions that create small security gaps before they become bigger problems.
Detection focuses on behavior patterns, not content or productivity. Your team's privacy stays intact while you get the visibility you need.
See how Presence detects these scenarios in real-time. Email contact@pistachioapp.com to book a 15-minute demo and we'll walk through exactly how it works in your environment.