Security awareness training for small and medium businesses used to be straightforward. Annual training sessions worked when phishing emails had obvious red flags: poor grammar, suspicious sender addresses, generic greetings. Employees could spot these threats with broad training, and a yearly refresher was enough.
That approach no longer works.
AI has changed phishing attacks. Phishing emails generated by AI models show a 67% higher click-through rate than traditional attempts[1]. Modern phishing emails are personalized, contextually accurate, and nearly identical to legitimate business communications. Annual cybersecurity training teaching employees to spot outdated threat patterns isn't preparing them for AI-powered attacks they'll face.
The data on annual security awareness training effectiveness is damning. Research from the University of Chicago and UC San Diego found "no evidence that annual security awareness training correlates with reduced phishing failures"[2]. Employees who had just completed training clicked phishing simulations at the same rates as those who hadn't trained in months.
Why Annual Security Training Fails: The Forgetting Curve
The problem isn't that employees don't pay attention during training. It's that human memory doesn't work the way annual training assumes it does.
Research on the forgetting curve reveals that within just 24 hours, most learners forget 70% of new information, and within a week, retention drops to a mere 25%[3]. Within 1 hour, learners forget an average of 50% of the information presented[4]. Even when training works initially, performance remained strong up to about four months, but by six months without reinforcement, employees' phishing detection scores significantly deteriorated[5].
This isn't a failure of attention or effort. It's cognitive science. One-time learning doesn't stick without repeated exposure and practice. The Ebbinghaus Forgetting Curve illustrates that individuals can forget up to 80% of new information within a month if it's not reinforced[6]. Annual training asks employees to remember lessons for 12 months despite overwhelming evidence that retention drops dramatically after weeks.
The forgetting curve explains why so many organizations find themselves in a frustrating cycle: deliver annual training, see compliance rates hit 95%, then watch employees click phishing simulations a few months later. The training box is checked, but behaviour hasn't changed.
Why Generic Security Awareness Training Doesn't Stop Real Phishing Attacks
Even if annual training solved the retention problem, most programs suffer from a more fundamental issue: they're generic.
“Too generic” was cited by 24% of employees as a major problem with their security training[7]. One-size-fits-all programs teach everyone the same content regardless of their role, the tools they use, or the actual threats they face. A finance team member working with invoices and payment systems faces different phishing tactics than an operations manager dealing with supplier communications. Generic training doesn't account for these differences.
The result? Training prepares employees to recognize obvious, outdated threats instead of the sophisticated, personalized attacks they'll encounter. If your phishing simulations use templates that are easy to spot, you're teaching pattern recognition for threats that no longer look like that. Employees learn to identify the fake emails in training, then fail to recognize real attacks that don't match those patterns.
This problem compounds when organizations use the same simulations for everyone. AI-generated attacks have evolved from being 31% less effective than human-crafted attacks in 2023 to 24% more effective by early 2025[8]. Attackers are using AI to personalize campaigns based on publicly available information: LinkedIn profiles, social media posts, company websites. They're crafting messages that reference the recipient's actual role or industry context. Generic training that ignores this reality leaves employees unprepared.
What Makes Security Awareness Training Effective: 3 Key Elements
If annual, generic training doesn't work, what does? The evidence points to three critical elements: frequency, personalization, and realism.
1. Frequency
Experts recommend at least quarterly training, with refreshers every 4-6 months Techclass. Better yet, shift from infrequent training marathons to continuous micro-learning. Annual training doesn't change behavior. Monthly five-minute exercises do [9]. Short, regular exposures combat the forgetting curve by reinforcing lessons before they fade from memory.
But you don't have capacity to create custom training materials and simulations for each employee. That's where automation becomes essential. Continuous training only works if it runs without manual campaign scheduling, content updates, or completion chasing. The moment training requires constant administrative effort, it stops happening consistently.
Your IT team is already managing infrastructure, handling support tickets, and keeping systems operational. Adding manual training management to that workload means it won't get done, or it becomes a checkbox exercise that doesn't improve security.
2. Personalized
Training should adapt to the individual. Someone who consistently spots phishing attempts needs more sophisticated simulations. Someone who's struggling needs reinforcement at their current level, not content that's too advanced to be useful.
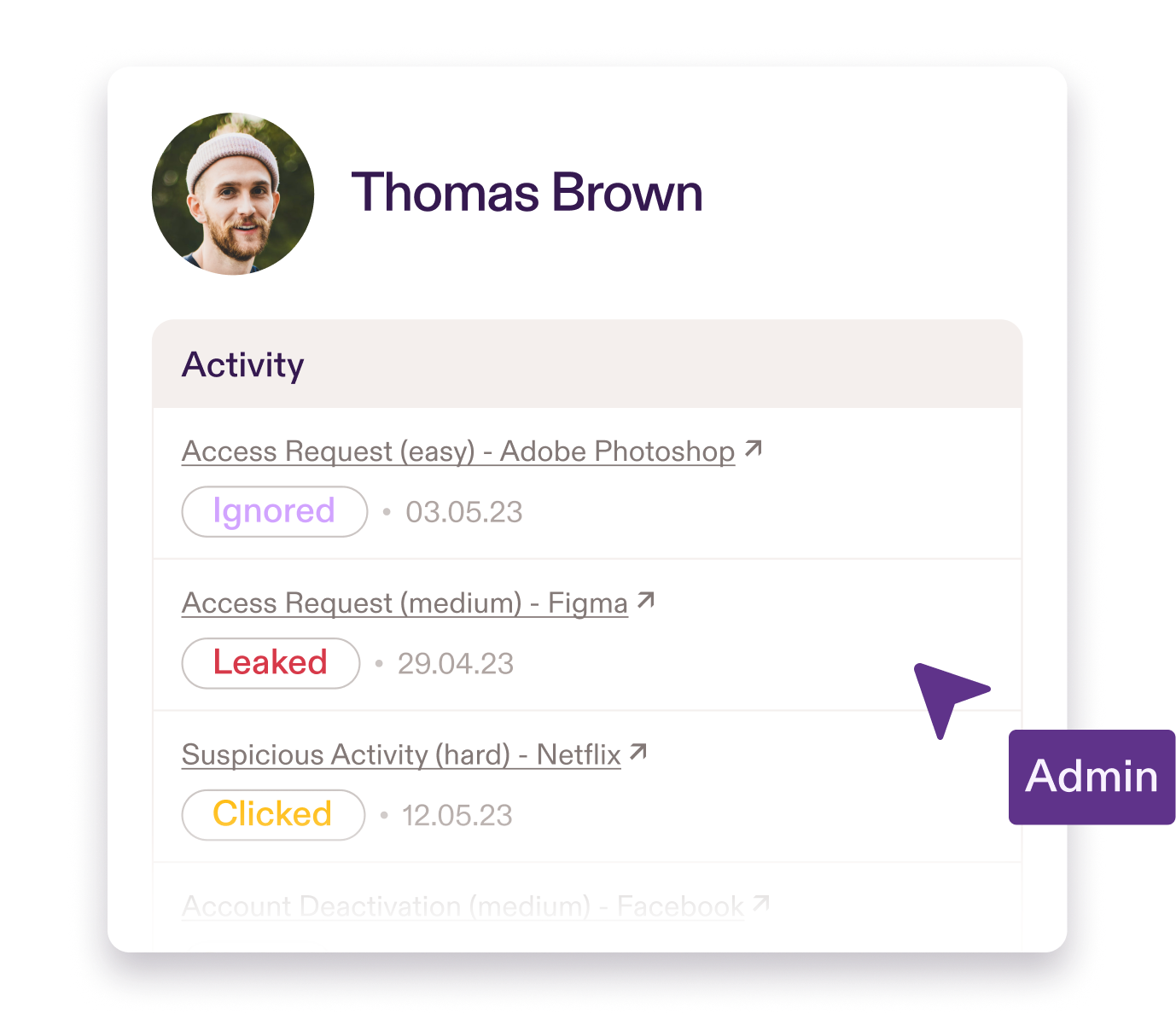
Effective training adjusts both difficulty and frequency based on each employee's past performance to provide just the right level of challenge. If someone is catching most phishing attempts, they receive more sophisticated simulations less frequently. If someone is clicking through threats, they get more frequent, targeted training at an appropriate difficulty level until their skills improve. This adaptive approach keeps training relevant without overwhelming people who already have strong awareness or boring people who need more challenge.
Personalization also means matching training to context. A finance team member should see phishing simulations that mimic invoice scams, payment redirects, and vendor impersonation (the attacks they'll face). An operations manager should train on supplier communication threats and shipment notification scams. When training feels relevant to employees' daily work, engagement improves and lessons stick.
The tools employees use matter too. Organizations running Microsoft environments face phishing attempts via Outlook and Teams. Training that only simulates email threats misses half the attack surface. Effective programs need to cover every channel where threats arrive.
3. Realistic
If employees can easily spot your training simulations, you're not preparing them for real attacks. Modern phishing doesn't have obvious red flags. It references legitimate projects, uses correct company terminology, and arrives from addresses that look plausible.
Sophisticated AI-generated spear phishing using OSINT data succeeds approximately 54% of the time[10]. The only way to prepare employees is to simulate these realistic threats in a controlled environment. That means phishing emails that reference their actual role, industry-specific scenarios, and attacks that match current tactics attackers are using.
Realism also means consequences that mirror reality. Clicking a phishing simulation should trigger immediate, contextual feedback explaining what went wrong and why. This turns mistakes into teaching moments instead of just collecting failure data.
Moving from Annual Training to Behaviour Change
Annual training persists because it satisfies compliance requirements with minimal effort. Schedule one session, track completions, generate a report for auditors.
But organizations conduct security awareness training on an annual basis too often to check a box to comply with standards and regulations, not to reduce risk and improve security[11]. Compliance doesn't equal effectiveness. Meeting the letter of a requirement while leaving your organization vulnerable isn't really compliance at all.
What changes behaviour is consistent exposure to realistic threats, personalized to each employee's context, delivered frequently enough that lessons stick. This doesn't happen through annual training sessions. It happens through automated systems that run continuously in the background, adapting to user performance and covering the actual attack vectors your team faces.
Practice delivers this approach. It deploys in 10 minutes, integrates with your Microsoft environment, and runs continuous phishing simulations across email and Teams. Simulations personalize based on each user's role, tech stack, and performance, automatically adjusting difficulty as skills improve. Micro-learning scenarios train employees on real threats in 30-60 seconds. Policy management and acknowledgment tracking happen automatically. Audit-ready reporting for ISO 27001, NIS2, and Cyber Essentials is built in.
No annual sessions to schedule. No generic content that doesn't match your reality. No manual campaign management. Just continuous, personalized training that changes behaviour.
“Traditional phishing training feels like a box-ticking exercise, but Pistachio builds real skills over time. My users enjoy the tests, get instant feedback, and even brag about spotting fake emails. I can see a clear improvement in awareness and vigilance that lasts all year, not just after a one-off training session.”
Joseph Cunningham
Head of IT Security & Support
OOONO
See how Practice builds lasting resilience in your team. Email contact@pistachioapp.com to book your 15-minute demo.