"We're too small to be targeted by hackers." This assumption might have been true 10 years ago, but as the data shows, hackers no longer care about an organization’s size.
According to recent industry findings, nearly 70% of phishing-related breaches[1] now hit small and mid-market businesses. In 2024 alone, 94% of SMBs reported being attacked, up from 73%[2] just the year prior. These aren't isolated incidents. They're a clear pattern: attackers have shifted their focus to non-enterprise companies, and the data shows it's working.
The urgency is real enough that the UK government recently launched a campaign urging companies to "lock the door on cyber criminals," following new figures estimating cybercrime costs UK businesses £14.7 billion a year[3], with around half of small businesses reporting a breach or attack in the past 12 months.
The reason? You have the data they want and lack the processes to protect it. And with the addition of AI, it’s easier than ever for attackers to automate and scale their operations.
AI Has Changed the Economics of Cybercrime
Attacking non-enterprise companies used to require effort. Attackers had to craft convincing phishing emails, research targets, and manually manage campaigns. Now, AI handles much of that work automatically.
Phishing emails generated by AI models show a 67% higher click-through rate than traditional attempts[4] because they mimic tone, context, and phrasing convincingly. These aren't obviously suspicious emails with poor grammar and generic greetings. They're personalized messages that reference your industry, your tools, and your work patterns.
81% of cybercriminals are now leveraging AI-powered tools to improve attack success rates[5], making traditional security measures less effective. AI allows attackers to scan the internet for vulnerable systems at scale, craft convincing phishing campaigns in minutes, and adapt their tactics based on what works. What used to be time-intensive is now automated and effective.
For non-enterprise companies, this creates a vulnerability. Attackers are using AI to scale and refine their operations. But most organizations are still relying on annual training sessions, hoping employees can spot threats that could now pass as legitimate communications.
Why Attackers Prefer Non-Enterprise Targets
Cybercriminals aren't personal. They're pragmatic. They scan the internet for vulnerabilities, and when they find an organization without strong email security, multi-factor authentication, or regular security training, they strike. Size doesn't protect you. In fact, it often makes you more vulnerable.
Phishing and credential theft account for roughly 73% of breaches[6], making human error the top risk factor across organizations of all sizes. But non-enterprise companies face a specific set of conditions that make these attacks more successful:
Limited security resources. You don't have a Security Operations Center. You don't have dedicated analysts monitoring for threats 24/7. Your IT team is managing infrastructure, handling support tickets, and keeping systems operational. Security awareness training often falls to the bottom of the priority list because there's no one with the bandwidth to manage it.
The "we're not a target" mindset. Despite the statistics, 26% of SMBs agree with the statement "we're too small to be targeted by hackers"[7]. This false sense of security means companies don't take basic protective steps like regular phishing simulations or enforcing strong password policies. Research from Yubico found that 57% of employees at small businesses with 1-99 staff received no cybersecurity training in 2025[8], leaving many unprepared for AI-driven phishing and social engineering. Attackers know this and exploit it.
Easier access, same valuable data. You hold customer payment information, employee records, supplier contracts, and intellectual property. To an attacker, that's just as valuable as enterprise data, but it's behind weaker defences. For attackers looking to collect significant funds, it's often easier to demand smaller amounts from 20 businesses than to attack one large company[9].
Supply chain vulnerability. If you work with larger organizations, you become an entry point. Attackers target non-enterprise suppliers and partners specifically because they know your systems connect to bigger, more secured networks. Compromising your account can open doors to your clients.
The Real Cost of Getting Security Awareness Wrong
The financial impact isn't theoretical. The average cost of a data breach for small firms reached $3.3 million in recent studies, with median incident costs around $8,300[10]. For many non-enterprise organizations, that's existential. According to research, 61% of SMBs worry that a serious cybersecurity attack could put them out of business[11].
But the damage extends beyond immediate financial loss. There's downtime while you recover systems. There's customer trust you'll never fully regain. There are regulatory fines if you're subject to compliance requirements. And there's the time your team spends responding to the incident instead of running the business.
What makes this worse? 82% of breaches are caused by humans[12], whether through clicking phishing links, using weak passwords, or falling for social engineering tactics. The good news is that human behaviour can change. The challenge is that it requires ongoing training, not a one-time session employees forget within hours.
Why Annual Training Isn't Enough
Most organizations that do security awareness training follow the same pattern: schedule an annual session, send everyone through the same generic content, check the compliance box, and move on.
This doesn't work. The median time for users to click on a phishing simulation link is just 21 seconds[13]. Your employees aren't clicking because they're careless. They're clicking because AI has made phishing emails nearly impossible to distinguish from legitimate communications. Generic training that teaches people to look for obvious red flags doesn't prepare them for attacks that no longer have obvious red flags.
The problem compounds when you consider that fewer than 1 in 5 small businesses conduct phishing simulations at least once per quarter[14]. Without regular, realistic exposure to what modern AI-powered phishing looks like, your team won't recognize it when it arrives in their inbox or Microsoft Teams.
What Good Security Awareness Training Looks Like
Effective security awareness training isn't about checking a compliance box. It's about changing behaviour through continuous, realistic exposure to the threats your team faces.
This means training should be:
Ongoing: Training needs to happen regularly, not once a year. People forget. AI-powered threats evolve constantly. Continuous reinforcement is the only way to build lasting awareness.
Personalized: A finance team faces different threats than an operations team. Training should reflect the actual tools and threats your team encounters in their Microsoft environment, whether that's Outlook, Teams, or other collaboration tools.
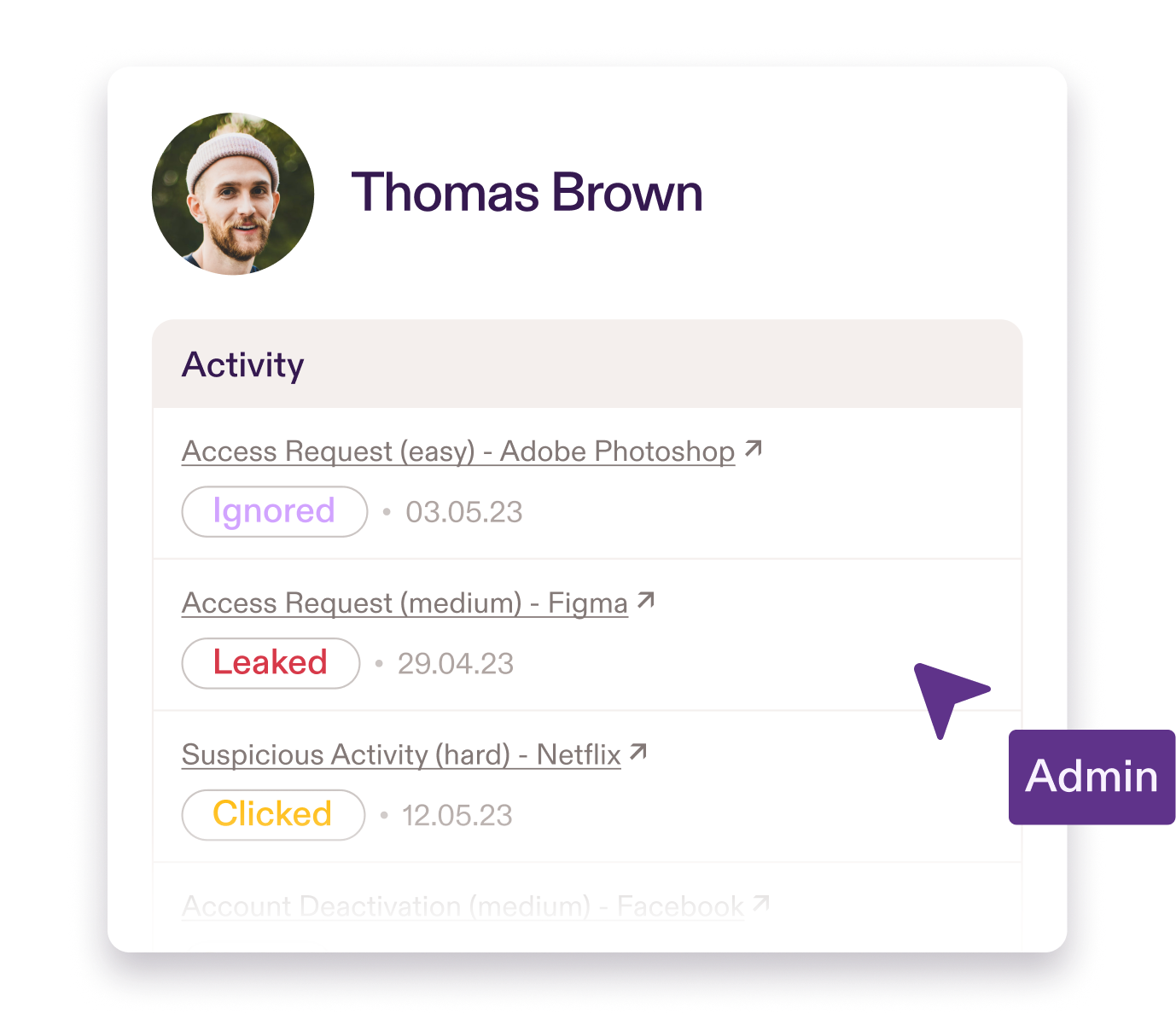
Realistic: If your phishing simulations are easy to spot, you're teaching people to recognize fake threats, not real ones. Simulations should mirror current AI-powered attack tactics across email and messaging platforms, so when the real thing arrives, your team is prepared.
Adaptive: Difficulty levels and frequency should be adapting based on employee behaviour, so their being challenged at the right level.
Integrated: Training that disrupts work gets ignored. Micro-learning (30-60 second modules) drives better engagement and retention than hour-long video courses people skip through.
Automated: If running security training requires scheduling campaigns, chasing completions, and generating reports manually, it won't happen consistently. The administrative burden kills momentum, and training falls by the wayside when other priorities arise.
It’s Time to Build Resilience to Phishing
Non-enterprise companies are being targeted more aggressively because attackers know the defences are weaker. AI has amplified this gap, making attacks faster, cheaper, and more convincing than ever before. The statistics make this clear. What's less clear to many organizations is that the solution isn't complex or expensive. It's consistent.
Security awareness training works when it's continuous, realistic, and doesn't require a dedicated team to manage. Your employees need to have the tools to recognize threats that AI is making harder to spot.
Practice runs security awareness training automatically. It deploys in 10 minutes, integrates with your Microsoft environment, and personalizes phishing simulations across email and Teams based on your tech stack and each user's performance. Micro-learning scenarios train employees on real threats in 30-60 seconds, not hour-long sessions. Audit-ready reporting for ISO 27001, NIS2, and Cyber Essentials is built in. No campaigns to schedule, no users to chase, no templates to update.
Security awareness without the workload.
See how Practice builds resilience in your team. Email contact@pistachioapp.com to book your 15-minute demo.